Resources
- Latest Resources
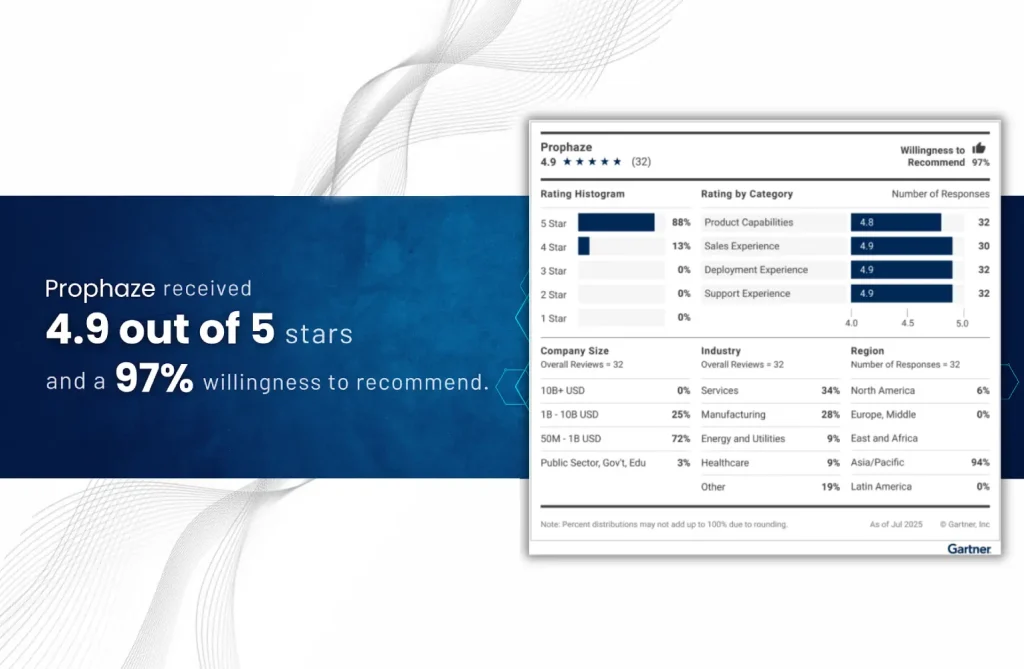
“Voice of the Customer” 2025 for Cloud Web Application and API Protection
- Blog
API gateways play a key role in today’s digital security, acting as an essential safety
- Blog
GraphQL API security is critical to protecting your application from threats and vulnerabilities. GraphQL, with
- Blog
Identity and Access Management (IAM or IdAM) is a set of policies, procedures, and technologies
- Blog
Automation is key to business efficiency and security in today’s rapidly evolving digital environment. An
- Blog
The smooth and connected digital world is also an arena for cybercriminals who organize account
- Blog
HTTPS cookies, essential for website functionality and user experience, become a security liability when not
- Blog
Insider threats refer to security risks caused by people inside an organization who are authorized
- Blog
Cross-Site Request Forgery (CSRF) is an attack method that tricks users into performing an unwanted
- Blog
SlowLoris DDoS Attacks are a type of stealthy, low-and-slow layer 7 Distributed Denial of Service
- Blog
Multicloud involves utilizing two or more cloud service providers, such as Amazon Web Services (AWS),
- Blog
Continuous Integration (CI) focuses on frequently merging code changes from multiple developers into a shared
- Blog
Malicious Bots are computer programs that automatically perform the specified tasks for which they are