Resources
- Latest Resources
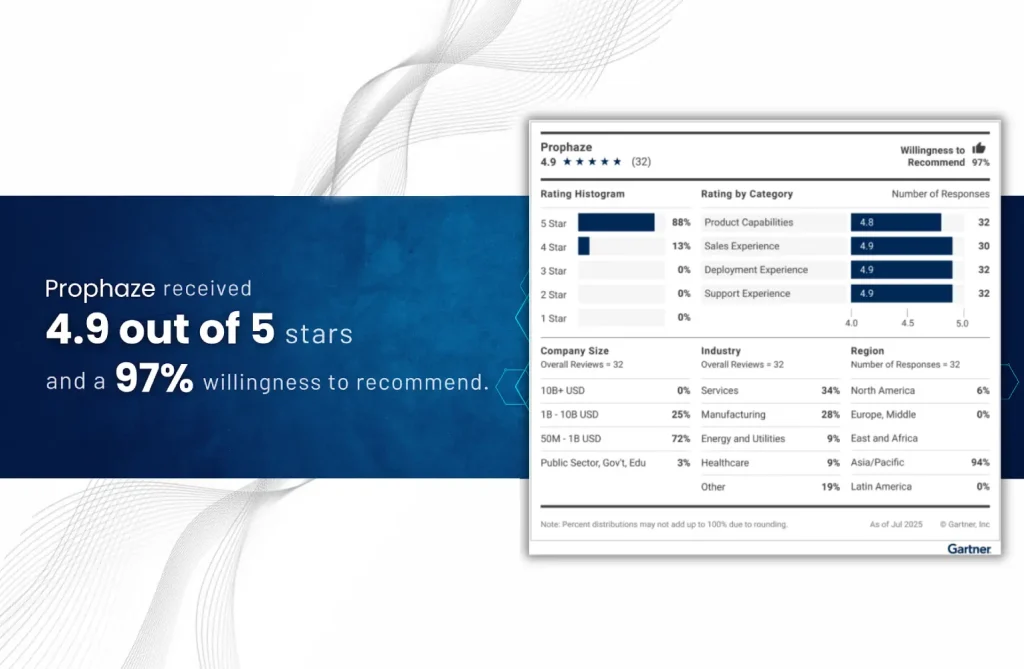
“Voice of the Customer” 2025 for Cloud Web Application and API Protection
- Blog
In a time where protecting digital privacy is crucial, end-to-end encryption (E2EE) has emerged as
- Blog
As businesses rapidly adopt cloud-native architectures—powered by Kubernetes, containers, and microservices—securing these highly dynamic environments
- Blog
In today’s interconnected world, securing web applications is not just optional; it’s essential. Web Application
- Blog
Bots account for nearly 50% of all internet traffic, and not all of them are
- Blog
In the current digital environment, safeguarding your web applications and APIs is imperative, not optional.
- Blog
In today’s hyper-connected digital ecosystem, cloud environments are the backbone of innovation—but they’re also prime
- Blog
APIs are the building blocks of modern digital ecosystems—powering mobile apps, SaaS platforms, IoT, and
- Blog
In a world where APIs serve as the foundation for digital transformation, ensuring their security
- Blog
Cloudflare WAF is a popular choice in the cybersecurity landscape, but it isn’t a one-size-fits-all
- Blog
In the fast-changing digital environment of 2025, it is essential to protect your online assets
- Blog
Web Application Firewalls (WAFs) are evolving. In 2025, protecting just against the OWASP Top 10
- Blog
Introduction to Security Model Rethink Traditional perimeter security models are no longer sufficient in an