Resources
- Latest Resources
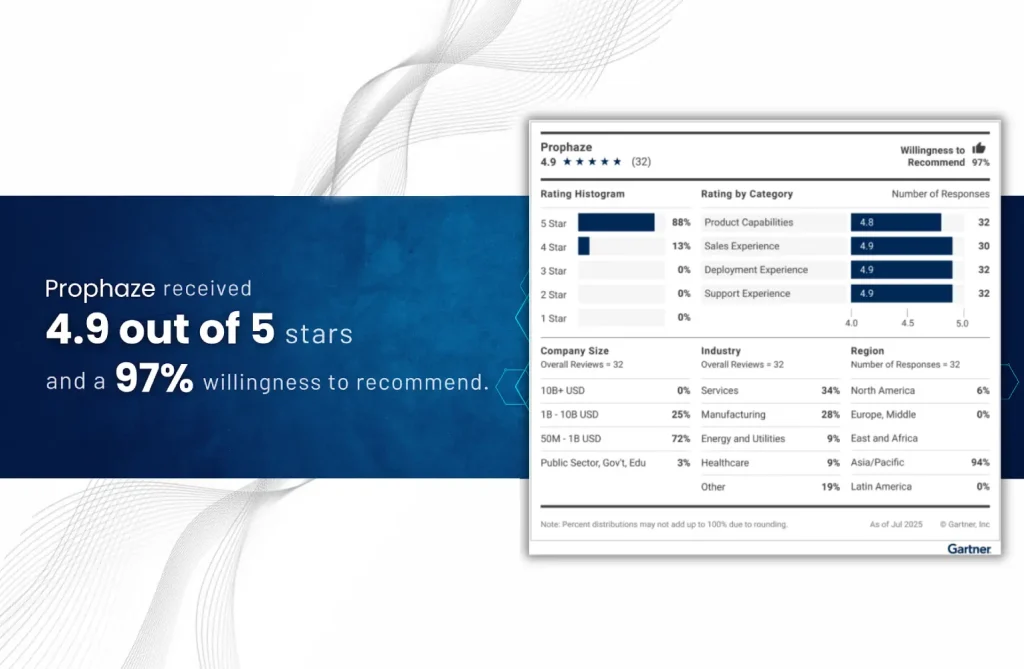
“Voice of the Customer” 2025 for Cloud Web Application and API Protection
- Blog
Continuous Integration (CI) focuses on frequently merging code changes from multiple developers into a shared
- Blog
Malicious Bots are computer programs that automatically perform the specified tasks for which they are
- Blog
Basic Mitigation Measures Some of the simple measures you can implement to block at least
- Blog
CoAP is a lightweight application-layer protocol designed specifically for IoT devices with limited resources, such
- Blog
In today’s interconnected world, managing a large number of remote devices efficiently and securely is
- Blog
TCP ACK Floods involve overwhelming a target network by inundating it with a barrage of
- Blog
Fragmented Attacks refer to a type of cyber assault that utilizes network packet fragmentation to
- Blog
TCP Connect Floods are a type of DDoS attack that aims to overwhelm a target
- Blog
Negotiation Floods are a type of DDoS attack that exploits network protocols’ negotiation processes to
- Blog
SSL what is termed as Secure Sockets Layer, the name itself depicts that a layer