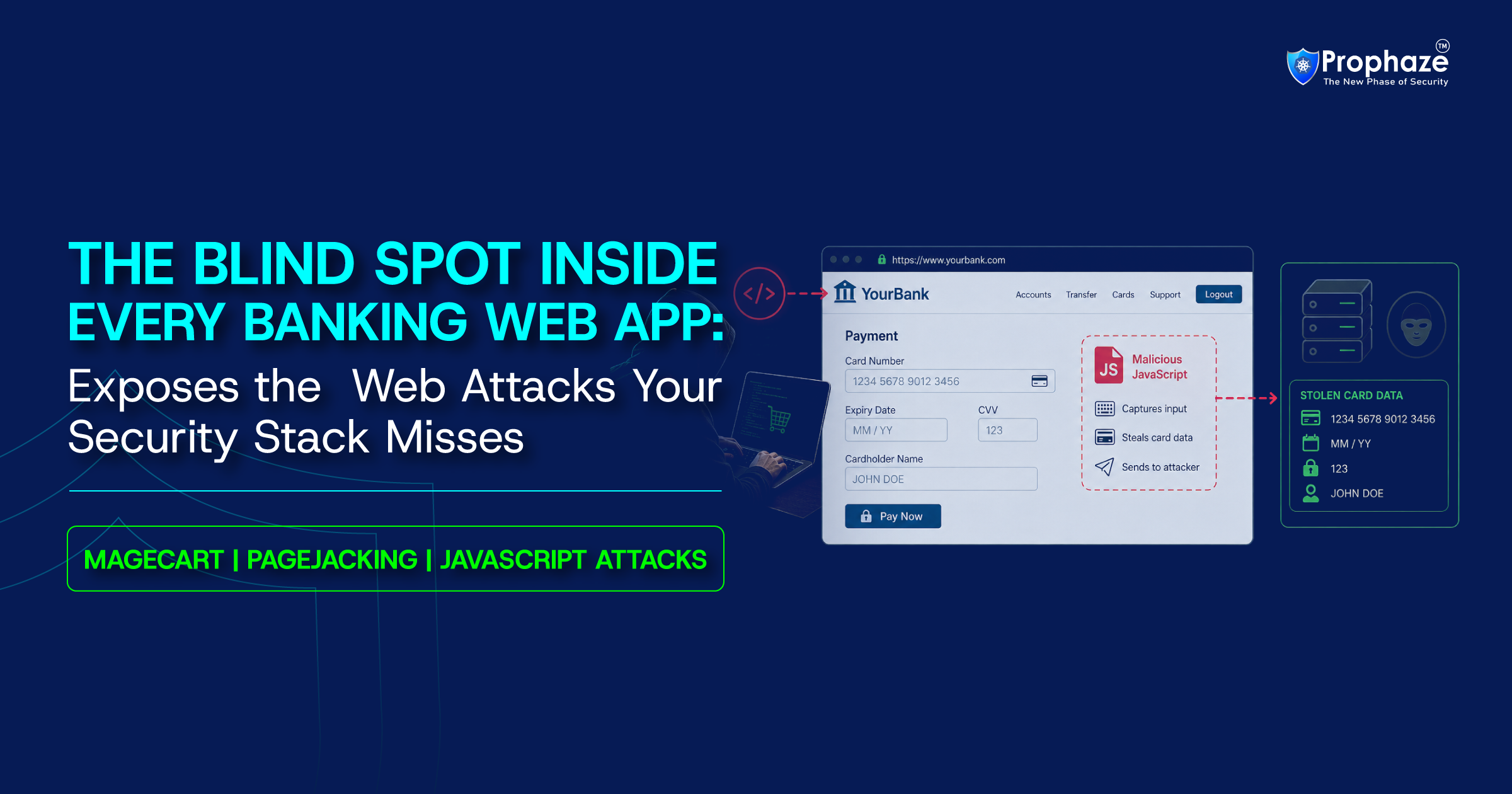
Stop Magecart Attack In Banking Applications Before They Expose Customer Data
What Is Magecart & Why Considering It Just An "E-Commerce Problem" Is The Most Dangerous Misconception in BFSI
What makes this critical for BFSI in 2026 is how widely it applies across banking interfaces:
- Online payment portals for cards, loans, and insurance
- Mortgage and personal loan application forms
- Net banking login and session flows
- Employee portals, HR systems, and internal stores
- Insurance claim and premium payment interfaces
- BNPL and embedded finance checkout journeys
- Fintech partner portals with web interfaces
The 2026 Magecart Attack Techniques Targeting Banking Systems
Attack 1: The WebRTC Skimmer, Bypassing CSP Entirely
-
Creates
RTCPeerConnectionwithout a signalling server (SDP handshake forged locally) - Exfiltrates data over UDP port 3479, not HTTP, invisible to WAFs and network tools
- Steals valid CSP nonces from existing legitimate scripts to inject its payload
-
Executes during
requestIdleCallback(browser idle time) to evade performance-based detection -
Falls back to
Function(code)()when CSP permitsunsafe-eval
Attack 2: The Invisible SVG Overlay, The Fake "Secure Checkout" Deception
- Uses invisible 1×1 SVG elements to trigger script execution
- Renders a fake checkout interface identical to the real one
- Captures card and payment data during form interaction
- Redirects users to the genuine checkout after data capture
- Leaves no visible UI anomaly or transaction failure
Attack 3: Google Tag Manager as a Skimmer Delivery Vehicle
Key Characteristics:
- Runs inside trusted GTM JavaScript containers on every page load
- Loads from allowlisted googletagmanager.com, bypasses CSP and WAF rules
- Blends seamlessly with legitimate analytics scripts
- Detects WordPress admin bars (wpadminbar) and hides from site administrator review
- Activates only on sensitive payment pages to minimise discovery risk
Why Traditional Security Cannot Detect Magecart
WAF Blindness:
CSP Failures:
- WebRTC uses UDP, CSP does not govern WebRTC
- GTM hijack loads from an allowlisted domain
- SVG overlay steals CSP nonces from legitimate scripts
PCI DSS 4.0 Gaps:
Server-side Scanning:
The Real Scale of Client-Side Banking Security Threats in 2026
- Magecart attacks surged 103% in just six months during 2024–2025.
- 269 million card records exposed via dark web in 2024, a 300% year-over-year increase across 11,000+ infected domains.
- A Magecart attack is attempted every 16 minutes globally.
- Global 6-network campaign (AmEx, Mastercard, Discover, Diners Club, JCB, UnionPay): continuously active since January 2022, over four years.
- January 2026 bank keylogger: only 1/97 security vendors detected the malicious domain.
- PolyShell mass exploitation: 471 stores compromised in one hour (March 30, 2026).
- ANY.RUN banking-specific campaign: 24+ months active, 100+ domains, 12+ countries.
- Detection timelines: British Airways, 2 weeks; Ticketmaster, 4 months; 2022 campaign, 4 years.
How Prophaze Secures Banking Applications Against Client-Side Attacks
Injection Vector Protection
Virtual Patching for Zero-day Exposure
AI-driven Behavioral Threat Detection
Bot and Automated Attack Prevention
Outbound Exfiltration Detection
PCI DSS 4.0 Compliance Support
What BFSI CISOs Must Do This Quarter
-
Monitor third-party JavaScript risk financial sector on every page that handles financial data. Not annually, continuously. GTM tags, analytics scripts, payment libraries, CDN assets. PCI DSS 4.0 makes this mandatory. Without real-time monitoring, you are both exposed and non-compliant.
-
Deploy tamper detection for payment pages under PCI DSS 4.0 Requirement 11.6.1. Alert within minutes when HTTP headers or payment page content change unexpectedly.
-
Restrict WebRTC-based exfiltration: If your banking applications do not use WebRTC for legitimate purposes, implement network-level blocking of unexpected outbound UDP. Browser-level CSP controls for WebRTC are not standardised, this is a WAF and network layer problem.
-
Patch PolyShell immediately: If you run Magento or Adobe Commerce anywhere, employee stores, partner portals, integrated payment flows, mass exploitation has been active since March 19, 2026. No full official patch exists for all production versions. Use WAF virtual patching as your immediate bridge.
-
Include internal and employee-facing sites in your security scope: The January 2026 bank keylogger ran on an employee merchandise store. Internal sites handling credentials or payment data carry the same Magecart exposure as customer-facing portals, and receive far less security scrutiny.
-
Publish a
security.txtfile and maintain a clear security contact. When a researcher discovers active malware on your payment portal, make it possible for them to reach you in under an hour.
Quick Reference: 2026 Magecart Threat Summary for BFSI
Can Your Banking Security Stack Detect Client-Side Magecart Attacks in Real Time?
Most BFSI security tools still focus on server-side threats, while Magecart operates silently inside the browser through trusted scripts, GTM containers, and third-party JavaScript. If your platform cannot detect malicious script behavior, monitor outbound browser activity, or identify supply chain compromise in real time, your banking applications remain exposed.
- One injected script. One trusted dependency was abused. Would you catch it before the data leaves the browser?