Resources
- Latest Resources
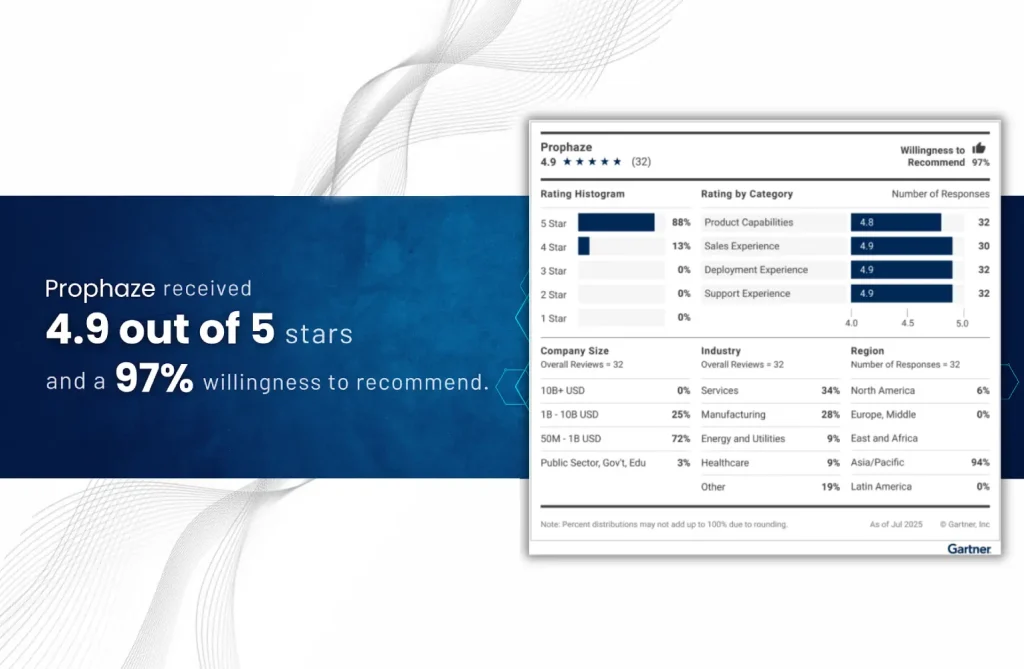
“Voice of the Customer” 2025 for Cloud Web Application and API Protection
- Blog
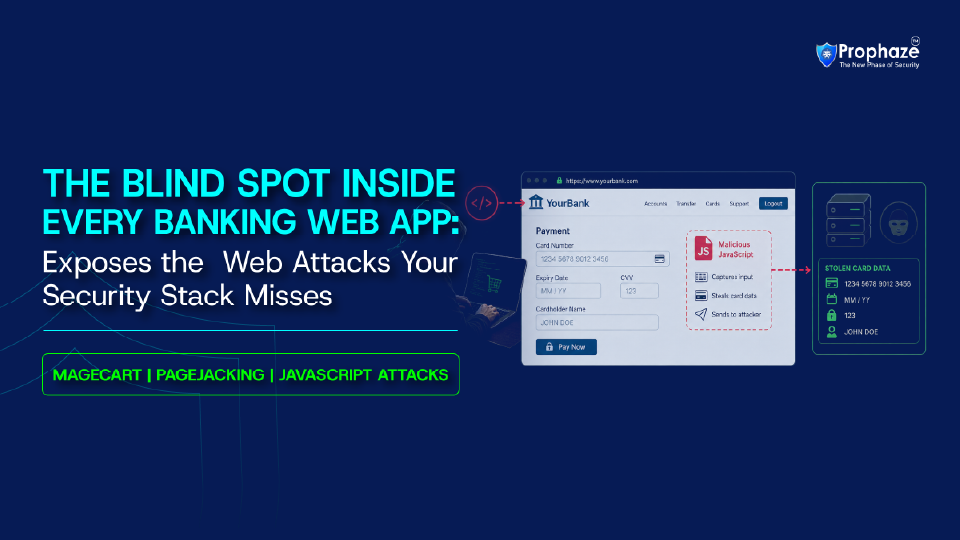
Stop Magecart Attack In Banking Applications Before They Expose Customer Data Magecart attacks on banking
- Blog
Application and API Security for BFSI: Why Traditional Defenses Are Failing Application and API security
- Blog
The Attack Nobody Is Logging: Server-Side Request Forgery in Healthcare Behind your perimeter firewalls, deep
- Blog
The Pen-and-Paper Reality: The Urgent Need for Web Application and API Security in Healthcare Web
- Blog
Exposing Partial Inspection Evasion in Modern WAFs In 2026, organizations widely deploy Web Application Firewalls
- Blog
Ingress NGINX Retirement: What Happens After the End of Life (EOL) Ingress NGINX Retirement is
- Blog
The Security Gap No Single-Environment WAF Can Close Enterprise hybrid WAF solutions have become essential
- Blog
Why API Disovery Matters in Modern Infrastructure Modern digital infrastructure is mainly driven by APIs
- Blog
Introduction Most modern attacks do not target the network layer. They target web applications, login
- Blog
Introduction Google Cloud Armor secures your infrastructure perimeter. But modern APIs, GKE workloads, and microservices
- Blog
Artificial intelligence is no longer limited to generating responses or summarizing information. Modern AI systems
- Blog
Kubernetes Web Application and API Protection (KWAAP) has become essential as traditional WAFs only secure