Blogs
- Latest Blog
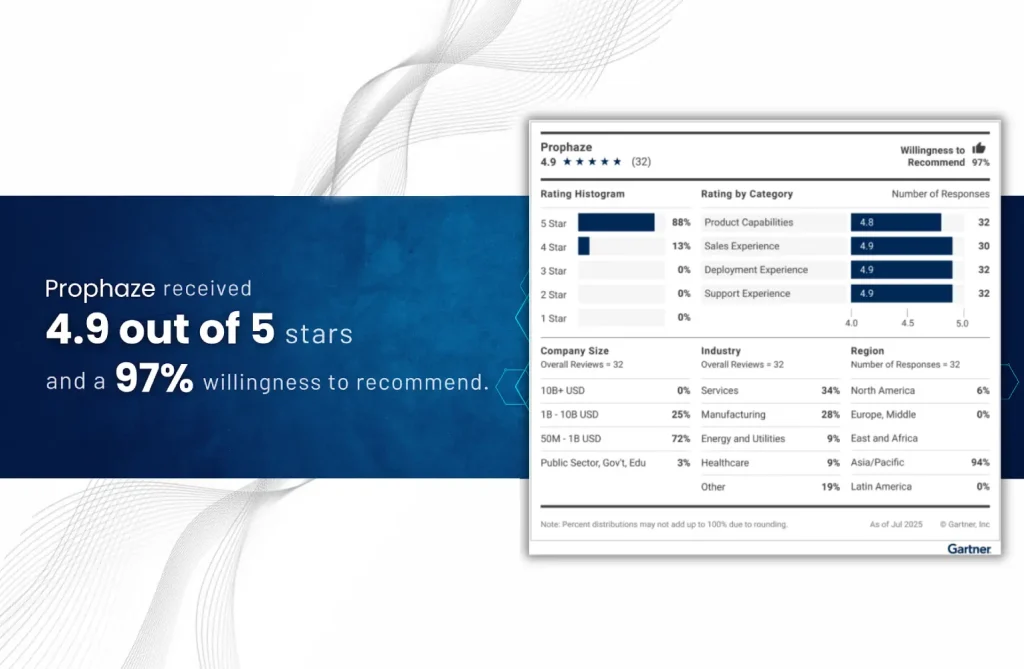
“Voice of the Customer” 2025 for Cloud Web Application and API Protection
- Blog
Introduction In the first half of April 2025, cybersecurity threats have escalated in both volume
- Blog
CVE-2025-29927 CVSS Score: 9.1 High Severity A newly discovered high-severity vulnerability in Next.js (CVE-2025-29927) is
- Blog
As digital risks multiply and enterprise environments become more complex, cyber insurance is fast becoming
- Blog
A recently uncovered web skimming scheme is elevating online fraud by leveraging an outdated Stripe
- Blog
SSL/TLS encryption forms the foundation of secure online communications; however, misconfigurations can expose vulnerabilities to
- Blog
The cybersecurity landscape continues to evolve with adversaries deploying new and advanced malware loaders to
- Blog
Why Real-Time DDoS Detection Tools Are Essential in 2025 DDoS attacks are becoming more frequent
- Blog
Integrating a Web Application Firewall (WAF) into DevSecOps pipelines ensures continuous security, real-time threat mitigation,
- Blog
APIs are the backbone of modern applications, enabling seamless communication between systems. However, their increasing
- Blog
The cybersecurity landscape in 2025 has seen a dramatic rise in sophisticated cross-domain attacks. These
- Blog
The cybersecurity landscape in 2025 is evolving rapidly, driven by AI advancements, increased cloud adoption,
- Blog
User and Entity Behavior Analytics (UEBA) is a cybersecurity solution that uses advanced analytics to