Blogs
- Latest Blog
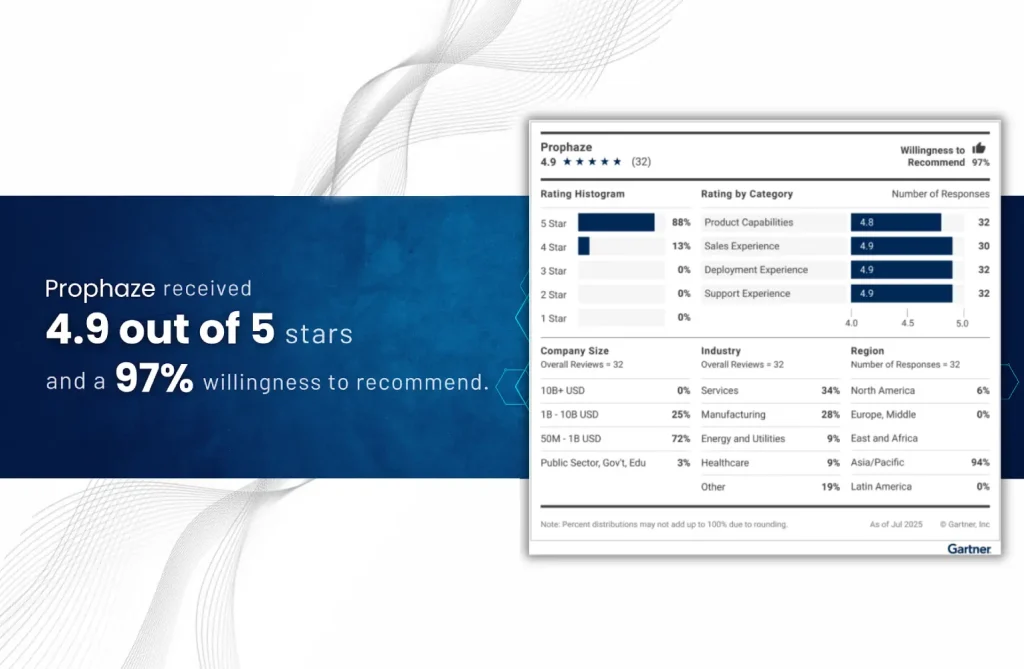
“Voice of the Customer” 2025 for Cloud Web Application and API Protection
- Blog
Why Cybersecurity Compliance Matters More Than Ever In today’s rapidly digitizing world, cybersecurity has transitioned
- Blog
As cyberattacks grow in complexity and velocity, network security in 2025 is no longer just
- Blog
Zero Trust is no longer a buzzword — it’s the bedrock of modern cybersecurity. As
- Blog
Introduction to Evolving Landscape of Intrusion Detection In the current complex cybersecurity scenario, organizations experience
- Blog
Introduction to Cybersecurity Risk Management in 2025 As cyber threats continue to grow in complexity
- Blog
The Evolving API Threat Landscape APIs have become the foundation of digital transformation, facilitating quick
- Blog
The Evolution of SOCs in 2025 By 2025, Security Operations Centers (SOCs) will transform from
- Blog
Why DDoS Protection Is Critical in 2025 As businesses migrate more critical operations to the
- Blog
The Critical Role of Data Loss Prevention in Modern Cybersecurity In today’s world, data is
- Blog
In a time where protecting digital privacy is crucial, end-to-end encryption (E2EE) has emerged as
- Blog
As businesses rapidly adopt cloud-native architectures—powered by Kubernetes, containers, and microservices—securing these highly dynamic environments
- Blog
In today’s interconnected world, securing web applications is not just optional; it’s essential. Web Application











