As the cybersecurity landscape evolves rapidly in 2025, safeguarding web applications grows increasingly complex and vital. The rise in zero-day vulnerabilities, API exploitation, and advanced bot attacks necessitates that organizations assess and adopt the right mix of security tools.
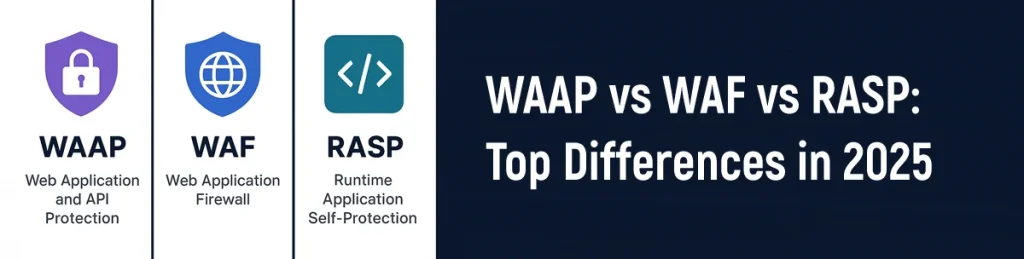
Three major solutions dominate modern AppSec strategies:
- WAF (Web Application Firewall)
- RASP (Runtime Application Self-Protection)
- WAAP (Web Application and API Protection)
This article highlights the fundamental differences between WAAP, WAF, and RASP, aiding organizations in making well-informed choices regarding their application security strategies for 2025.
WAAP vs WAF vs RASP: Top Differences in 2025
Scope of Protection
- WAF: Mainly centered on overseeing and filtering HTTP/HTTPS traffic to and from web applications. Its purpose is to prevent prevalent threats like SQL injection, cross-site scripting (XSS), and various attacks listed in the OWASP Top 10.
- RASP: Protection of individual applications by observing their behavior during runtime and detecting malicious activities in real time.
- WAAP: An all-encompassing solution that merges WAF and RASP functionalities, incorporating API protection, bot management, and DDoS mitigation.
2025 Insight: WAAP platforms are gaining popularity for their capability to manage complex architectures, such as microservices and widespread API utilization.
How Each Solution Works
- WAF: Functions at the edge, examining both incoming and outgoing traffic with rules and signature detection before reaching the application.
- RASP: Functions within the application integrate into its codebase or runtime to identify and thwart attacks based on real application behavior.
- WAAP: Utilizes perimeter and in-application defenses, incorporating AI and behavioral analysis to identify intricate threats.
2025 Insight: WAAP’s hybrid detection model enhances its ability to identify sophisticated attacks often overlooked by traditional perimeter defenses.
Intelligence & Threat Detection Capabilities
- WAF: Employs fixed rules and established signatures for recognized vulnerabilities, with constrained contextual awareness.
- RASP: Provides insight into application behavior and helps thwart logic-based and zero-day attacks.
- WAAP: Utilizes machine learning, evaluates threats, and implements adaptive threat detection to deliver a more intelligent and responsive security solution.
2025 Insight: The growing use of artificial intelligence in WAAP platforms has greatly enhanced their real-time threat detection and response abilities.
Deployment and Integration Flexibility
- WAF: Implemented at the network edge or in the cloud as either an appliance or a service. Typically straightforward to deploy.
- RASP: Integrated directly into the application, necessitating code-level integration. Ideal for custom-developed applications.
- WAAP: Whether cloud-based or deployed at the edge, it is designed for smooth integration in contemporary development settings, including both containerized and serverless infrastructures.
2025 Insight: WAAP solutions now provide improved compatibility with Kubernetes and API gateways, making them perfect for DevSecOps pipelines.
Ideal Use Cases
2025 Insight: WAAP is becoming the top choice for organizations with hybrid cloud setups, particularly those focusing on API security.
Logging and Visibility
- WAF: Offers a consolidated perspective on traffic across different applications, yet lacks insight into how those applications operate internally.
- RASP: Provides thorough logs regarding the internal performance and condition of a specific application.
- WAAP: Provides a cohesive and complete logging experience throughout applications, APIs, traffic patterns, and runtime anomalies.
2025 Insight: Security teams gain advantages from WAAP’s unified dashboards and up-to-date threat intelligence streams.
Cost and Implementation Complexity
- WAF: Affordable and fairly straightforward to handle, particularly in cloud environment models.
- RASP: Implementation is more complex, necessitating customization at the application level. Costs vary based on development effort.
- WAAP: Higher overall cost, but provides a superior return on investment for organizations with intricate security requirements.
2025 Insight: Although WAAP demands a greater upfront investment, it mitigates long-term risk exposure and frequently decreases operational costs by utilizing automation.
Role of AI & ML in Each Security Model
- WAF: Basic anomaly detection with preset parameters.
- RASP: Contextual threat detection driven by runtime behavior, featuring limited learning capabilities.
- WAAP: Advanced machine learning models aimed at behavioral analysis, identifying bots, and mitigating zero-day attacks.
2025 Insight: WAAP’s AI-based detection engines offer greater adaptability to new threats than WAF or RASP by themselves.
Which Security Solution Is Right for You?
Pro Tip (2025): Don’t rely on just one layer. Combine WAF + RASP + WAAP for a multi-layered AppSec posture.
In 2025, relying on a single security tool is insufficient. Organizations are adopting a layered security approach, combining WAF for filtering, RASP for runtime protection, and WAAP for comprehensive coverage against modern threats. Investing in the right combination of these technologies is critical for resilience in today’s fast-changing cyber landscape.
Prophaze offers an all-encompassing WAAP solution featuring AI-powered WAF, RASP, and enhanced API security, safeguarding contemporary applications and APIs from emerging cyber threats.